bpytop
A nice, beautiful alternative to htop, for monitoring your system.
bpytop is the same popular top++ but rewritten in python, from the original author.

bpytop
A nice, beautiful alternative to htop, for monitoring your system.
bpytop is the same popular top++ but rewritten in python, from the original author.

Anthias
Anthias is a free and open source digital signage management software.
Distributed as a Raspberry Pi image. And it will turn any TV into a powerful digital sign.

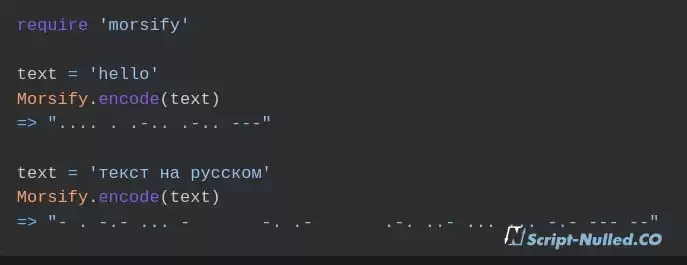
Mortify
Morsify is a library for converting text to Morse Code or vice versa.
Supports Latin and Cyrillic. Can generate a file in the format .wav
Fireball
Firejail is a sandbox program for isolated execution of graphical, console and server applications, which minimizes the risk of compromising the main system when running untrustworthy or potentially vulnerable programs.

👨💻 Purple Team.
• Purple Team — Helps the Red Team and Blue Team to be friends with each other, allowing the blue team to develop a strategy and technical measures to protect the infrastructure based on the vulnerabilities and shortcomings discovered by the red team. The task of such a team is to ensure and maximize the efficiency of all teams.

👤 OSINT. Search for a target by username.
• You've probably already encountered a service for finding a target using the username "whatsmyname", and if you haven't, be sure to pay attention. Recently, this resource has been updated and now we can search for information on the username on 576 popular sites. There is also an opportunity to search through the list of usernames, rather than going through the information for each individual query and re-perform the search.

The evolution of cybercrime. Analysis, trends and forecasts 2023.
• Group-IB has published an annual flagship report on current trends in cybersecurity and forecasts of the evolution of the threat landscape. In short, the direction of ransomware will retain its leadership in the ranking of cyber threats to business.

👨🏻💻 Steganography. Useful tools and resources.
• Steganography — for the first time this term was mentioned in 1499, and even then this word meant the transmission of information by keeping the fact of transmission secret. Oddly enough, nowadays steganography has not received widespread recognition among hackers, although it cannot be said that it has not been resorted to at all.

💬 true story... How I was hacked, my cryptocurrency wallets were emptied, and what Apple said.
• The story of how the creator of the website for job search in the field of cryptocurrencies cryptojobslist withdrew personal savings in cryptocurrency, simultaneously gaining access to Apple, Yahoo, Gmail and Telegram accounts with two-factor authentication enabled.

💬 true story... Christopher Rocancourt. The story of a famous conman and a $40 million fraud.
• At one time, writers Ilya Ilfov and Evgeny Petrov created a literary image of the “great combinator” Ostap Bender, who was able to "take" money in "four hundred comparative honest ways." One of his modern prototypes is Christophe Rocancourt. The only difference is that Bender called himself the son of a Turkish citizen, and the modern "combinator" is a descendant of Rockefeller.
💬 true story... What are the risks of pentesters trying to hack your company. Part 1.
• There have been no interesting stories from the lives of pentesters and social engineers for a long time, and to be honest, I missed this category. Today we will add another fascinating story to our list. Enjoy reading.

💬 true story from Group IB... False alarm.
• Today I found for you another and interesting story from Group IB, accepted reading:

💬 true story... The enemy is inside: how I got caught on insider redtiming.
• I had all the advantages. I've already been online. I was above suspicion. But they discovered my hacking, kicked me out of the network... and tracked me down physically.

💬 true story... Jonathan James. The story of a hacker who hacked the Pentagon and NASA at the age of 15.
The most difficult thing is not getting into the system, but learning and gaining knowledge so that you can then understand what can be done with it.

💬 true story... Social Engineering.
• Today we are talking about social engineering, namely the hacking of the American prison system with the help of #SI. Kevin Mitnick argued that no technology in the world can resist a social engineer, since people are easy to manipulate, and even in the most secure systems, it is people who can be the weak link.