Description: Shares Important and Common Topics on the forum
Version: 3.00
Supports: vBulletin 3.8.x release

Description: Shares Important and Common Topics on the forum
Version: 3.00
Supports: vBulletin 3.8.x release

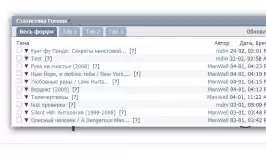
Title: [AJAX] imDM - Advanced Statistics v1.0.2
Description: Advanced statistics forum
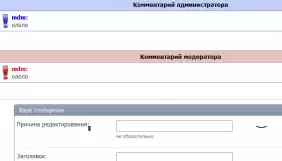
Title: VSQ - Comments Tags
Description: Allows you to add comments to messages from administrators and moderators
Installation:
1. Upload the contents of the upload folder to the forum folder
2. Import the product
PureVB - Defraction - style for the vBulletin 4.x forum is perfect for any topic of the forum.

Author: no name
Author's website:
Cute light blue style.
Works on the entire 3.8.x line
The author is me and Google.
Please do not delete the link from the footer, have a conscience)
Skin Type: Original
In the archive:
-installation instructions
-6 xml skin files
-PSD template
-Modules

Skin Type: Original
In the archive:
-installation instructions
-2 xml skin file
-PSD template
-Modules

Skin Type: Original
In the archive:
-installation instructions
-10 xml skin files of 5 colors
-PSD template
-Modules

Skin Type: Original
In the archive:
-installation instructions
-xml skin file
-PSD template
-Modules

Skin Type: Original
In the archive:
-installation instructions
-2 xml skin file
-PSD template
-Modules

In the archive:
- all PSD
- Skin color schemes
- Instructions for changing the skin color (English)
A high-quality rip of the Skylight template.

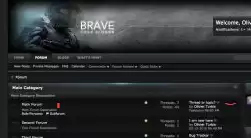
Template in dark colors for vBulletin 3.7.x - 3.8.x

One of the best skins for the forum from a good CompleteVB desk
The template is black, quite informatively coordinated and, of course, in high-quality execution.
There are sources in the archive.The template is original.

Template for vBulletin "Creative Creature"
